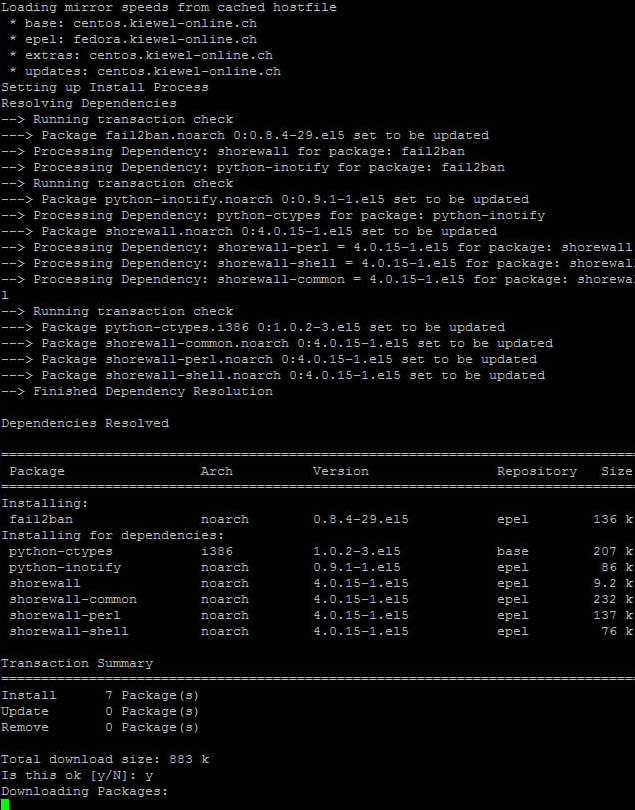
Installing fail2ban 8.4 on Centos
We will need the Epel repo for this one as this has the most updated version 8.4.29 ( you can check if something new is distributed here http://pkgs.org/download/fail2ban ).
You can find the latest release here http://fedoraproject.org/wiki/EPEL
Or you can download the 5-4 version via
wget http://download.fedoraproject.org/pub/epel/5/x86_64/epel-release-5-4.noarch.rpm
Then install with the command
Install gamin as it fixes a bug described at http://www.fail2ban.org/wiki/index.php/MANUAL_0_8
Then we install fail2ban
Make sure yum sees the 8.4 version from epel and not another version like rpmforge. If so disable it like yum --enablerepo epel --disablerepo rpmforge install fail2ban
Fail2ban Configuration
We will re-change the default path of the fail2ban log
and change the line logtarget
logtarget = /var/log/fail2ban.log
now we will need to either change the postrotate file for the fail2ban or rm it
personally i edited the file /etc/logrotate.d/fail2ban and changed the line between postrotate and endscript into
/usr/bin/fail2ban-client set logtarget /var/log/fail2ban.log 1> /dev/null || true
Now we will configure the jail.conf
Use a space for each ip you wish to prevent from being banned. We dont want to get ourselfes out right?
ignoreip = 127.0.0.1 xxx.xxx.xxx.xxx where x is your public static server ip.
Now about the rules, put enabled = true for each one you wish to enable and you need. Personally I have the following default rules set up with the changes noted bellow
[ssh-iptables]
logpath = /var/log/secure
[sasl-iptables]
logpath = /var/log/secure
[apache-tcpwrapper]
action = iptables-multiport[name=apache-auth, port="http,https"]
logpath = /var/log/httpd/*error_log
[apache-badbots]
logpath = /var/log/httpd/*error_log
After you have enabled each of the rules press
:wq and exit the editor.
Before we start the fail2ban service we will need to check each rule in order to make sure it is working and it will not break our configuration.
We can test eg ssh like fail2ban-regex /var/log/secure /etc/fail2ban/filter.d/sshd.conf
The general rule is
fail2ban-regex Full/LoggPath /etc/fail2ban/filter.d/rulename.conf
Or you can just use a script I have found in the net that automatically checks each of your enabled rules. Please note that the script checks all log files matched - new and old ones alike and returns a total number of fails matched. If no success message is not displayed do not worry, there is simply no attack found in your log files!
You will need to copy this file to a directory of your choice.
Then chmod it
and run it
If you see an error like “: /bin/bash^M: bad interpreter: No such file or directory”
edit the file and write
As a last step we will need to start the service and set it to auto start on boot.
chkconfig --add fail2ban
We can check if it is running ok with the commandIf something is preventing the service to start and fails you can try to start it byIt will then display the reason of failure so you can fix it in the jail.conf file.I did spend many hours trying to learn fail2ban and configure correctly various plug-insSo I hope you will find the above information useful!
1 comment
-
Comment Link
 Wednesday, 01 January 2014 23:24
posted by Arsia
Wednesday, 01 January 2014 23:24
posted by Arsia
Έχετε μια πολύ μεγάλη ιστοσελίδα www.digi - web.gr , Χαίρομαι που την παρατηρησα μέσω του yahoo .